Declarative. Isolated. Reproducible.
Lightning fast, local first sandboxes that secure the supply chain across devs, agents, and CI.
Get Started$ minimal run claude
Boot secure sandboxes in seconds. Outperform the Docker daemon.
Resolve dependencies in sub-seconds. End the BUILD+WAIT cycle.
Shared global caching. Prebuilt packages that won't bloat disks.
Repeatable execution. Identical sandbox configurations.
Hermetic environments for machines and humans
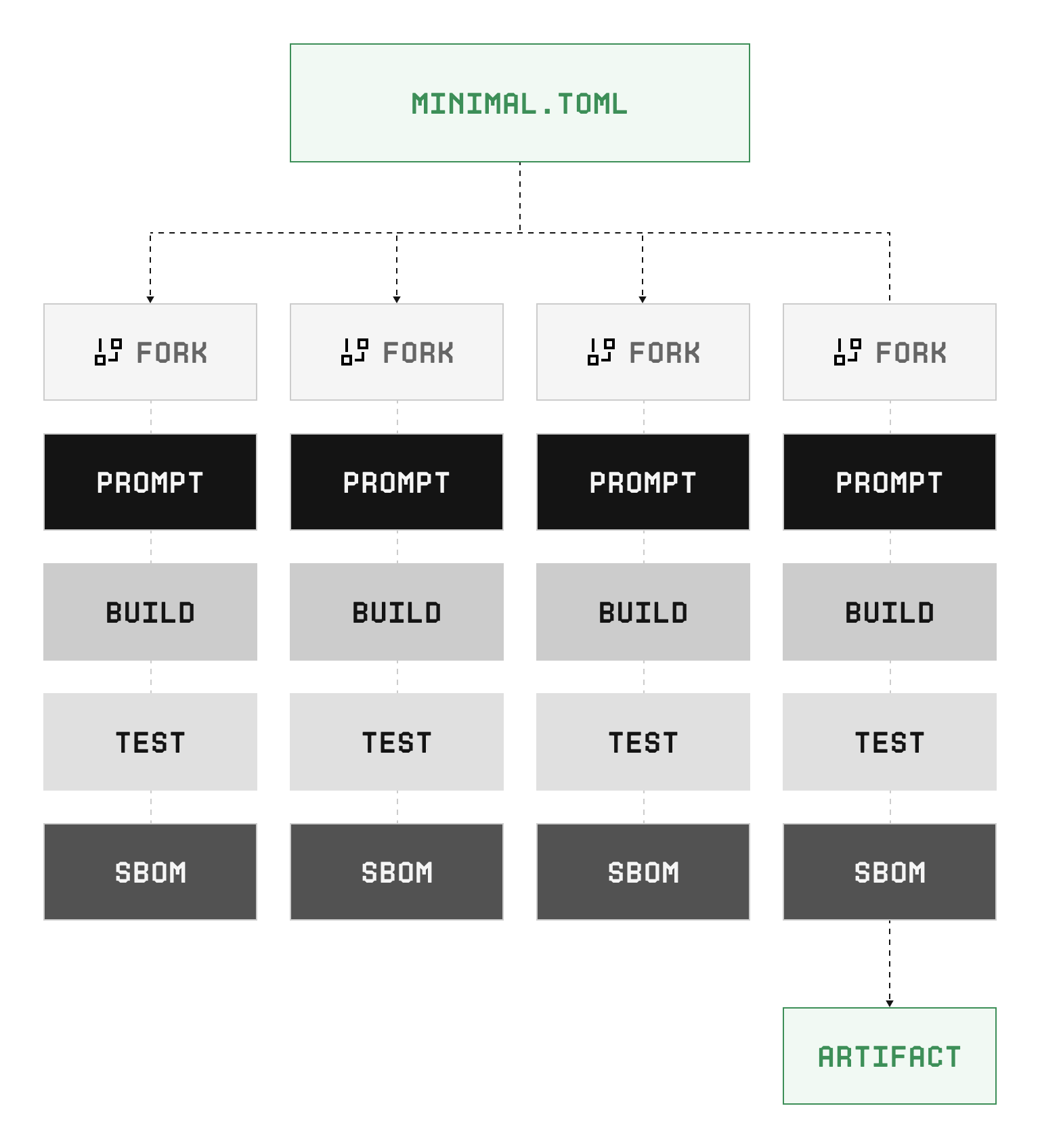
Minimal provides isolated, reproducible environments from a single configuration file that lives with your code across branches, forks, and worktrees.
Declare your packages and dependencies, run your tasks, and get the same result on every machine.
Under the hood: Linux namespace isolation, Nickel build specs with static types and contracts, content addressed caching across the dependency graph, SBOM generation, and cryptographic attestation.
Why we built Minimal
| Docker | Nix | asdf | mise | devbox | Minimal | |
|---|---|---|---|---|---|---|
| Sandboxed execution | ✓ | ✗ | ✗ | ✓ | ||
| Environmental parity | ~ | ✓ | ~ | ✓ | ||
| Daemonless | ✗ | ✓ | ✓ | ✓ | ||
| Declarative config | ✓ | ~ | ✓ | ✓ | ||
| Content addressed | ✗ | ✓ | ✗ | ✓ | ||
| Supply chain visibility | ~ | ~ | ✗ | ✓ | ||
| Rapid invocation | ✗ | ✗ | ✓ | ✓ |
Every existing tool asks you to pick a tradeoff: isolation or speed, reproducibility or simplicity, supply chain guarantees or usability.
We built Minimal because no existing tool delivers all of these together:
Real isolation, content addressed reproducibility, rapid invocation, and supply chain attestation.
Performance
$ minimal update
✓ base 1.0.0
✓ rust-toolchain 1.82.0
✓ openssl 3.4.1
✓ zlib 1.3.1
✓ curl 8.11.1
✓ nodejs 22.12.0
✓ python 3.13.1
... 7 more
Resolved in 1.2s
$Minimal hardlinks curated, provenance verified packages into a sandbox rootfs. Resolution happens once, before execution begins. Every dependency is prebuilt and available from cache without hitting an upstream registry.
- Dependency resolution from cache in seconds for most environments
- Only changed specs trigger rebuilds, that Minimal performs for you
- Environment assembly in milliseconds
- Parallel task execution across the dependency graph
Supply Chain Security
$ minimal dump --packages openssl
[{
"name": "perl",
"spec_hash": "51789e95...22b5401",
"is_prebuilt": false,
"is_collection": false,
"target": "amd64/linux",
"build_deps": [
{
"type": "local_file",
"filename": "build.sh",
"hash": "bfb6961f...5efeb684"
},
{
"type": "source",
"from": {
"type": "web",
"url": "gs://minimal-registry/perl-5.42.0.tar.xz",
"sha256": "73cf6cc1...bdbdd0c3"
}
},
...
]
}] Like Nix, Minimal curates its own package set. Unlike Nix, every package is provenance verified and tested before it enters the Minimal registry.
Your environment inherits that trust. Environments stay pinned by configuration and in turn, share a simple, robust upgrade path.
- SLSA Build L3 provenance on every package
- Full SBOMs. CycloneDX v1.5 with dependency graphs and PURLs
- VEX suppression with expiry and EOL detection
- Every upstream dependency verified before it enters the Minimal package registry
Ecosystem
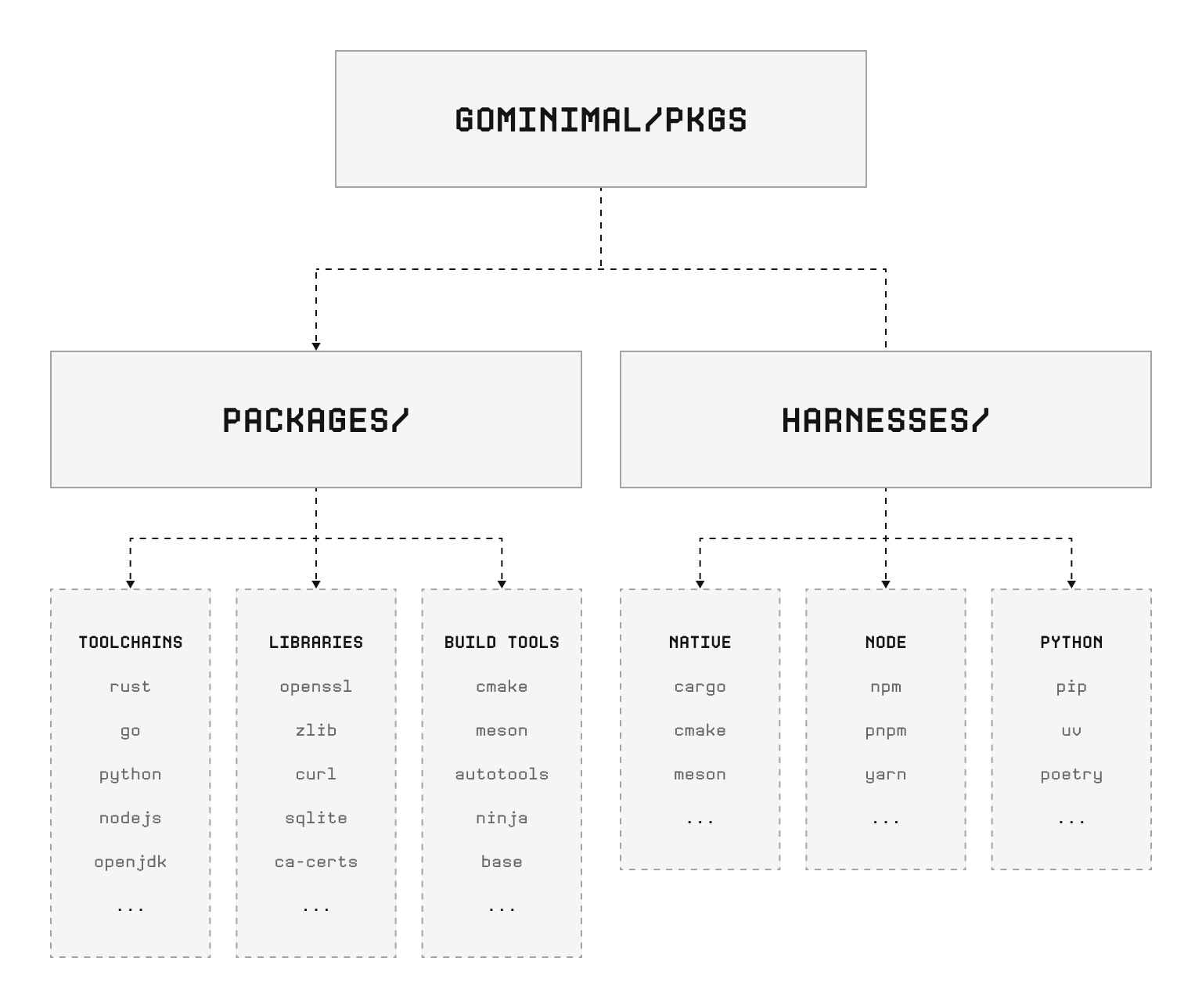
Minimal ships packages for:
- C/C++, Rust, Python, Java, Go, JavaScript/Node
- OpenSSL, zlib, curl, SQLite, and hundreds of common dependencies
- CMake, Meson, Autotools, Cargo, npm
Works with:
- Claude Code, Cursor, and other AI coding agents
- GitHub Actions, GitLab CI, Jenkins
- Developer laptops, Linux and macOS
Install
[upstream]
repo = "https://github.com/gominimal/pkgs"
branch = "main"
[harness]
use = "bun"
[defaults]
state_key = "dev"
[tasks.shell]
packages = ["base"]
exec = "bash -l"
[tasks.test]
packages = ["base"]
bash = "bun test"
[tasks.claude]
packages = ["base", "claude-code"]
exec = "claude --dangerously-skip-permissions"Minimal is available for early access locally. Install on macOS and Linux:
curl --proto "=https" --tlsv1.2 -fsSL https://go.minimal.dev/install.sh | sh Enterprise
# Enforce org-wide package policy
[policy]
require_provenance = true
require_sbom = true
max_vuln_severity = "medium"
[policy.packages]
allow = ["base", "rust-*", "nodejs-*", "python-*"]
deny = ["*-nightly"]
[policy.versions]
pin_major = true
eol_action = "block"
[cache]
shared = true
upstream = "cache.minimal.dev/acme-corp"
ttl = "30d"Minimal Cloud provides managed infrastructure for teams that need deterministic environments at scale. Shared caches, policy enforcement, and audit-ready attestation for SLSA L2+.
- Managed deployments. Reproducible environments that scale with your team
- Private cache. Dedicated, content addressed package cache shared across your fleet
- Policy enforcement. Define what packages, versions, and sources are permitted
- Audit trail. Full provenance chain for every environment and artifact
- Package update SLAs. Committed timelines for security patches and version upgrades